The work presents the results of a comparative analysis of stegosystems with algorithms for embedding in the least significant bit with matching and substitution for differences in the procedure for embedding additional information in the covering object and the resistance of the obtained steganograms to various methods of steganalysis.
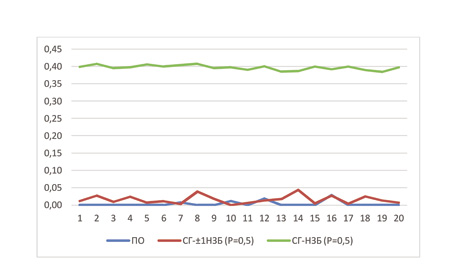
When using stegosystems with embedding algorithms in the least significant bit with matching and substitution, samples of steganograms with different embedding fractions were obtained for a sample of 200 covering objects. The results of the steganogram analysis on the steganogram data were analyzed, the obtained steganogram samples were compared to the detection of the presence of an additional information attachment using three steganalysis methods: visual attack, first-order statistical attack (chi-square attack) and second-order statistical attack (pairwise selective analysis attack). The presented example of images before and after a visual attack, for samples steganograms with attachments in the least significant bit with substitution and matching, with an investment fraction of 10%, 50% and 100%, allows to demonstrate the performance of the visual method steganalysis. The graphical representation of the results for first-and second-order attacks allows us to evaluate the effectiveness of the studied methods of stegoanalysis for stegosystems with algorithms for embedding in the least significant bit with matching and substitution. It is shown that a stegosystem with an algorithm for embedding in the least significant bits with matching is more resistant to detection attacks using modern methods of stegoanalysis. Conclusions are made about the possibility of applying the considered methods of stegoanalysis to the presented methods of stegosystems.